#
Securing your webhooks
Once your server is configured to receive payloads, it'll listen for any payload sent to the endpoint you configured. For security reasons, you probably want to limit requests to those coming from Airlock. There are a few ways to go about this--for example, you could opt to allow requests from Airlock's IP address--but a far easier method is to set up a secret token and validate the information.
#
Setting your secret token
You'll need to set up your secret token in two places: Airlock and your server.
To set your token on Airlock:
- Navigate to the group where you're setting up your webhook.
- Go to the group's 'Configure' page.
- In the 'Webhooks (Advanced)' section, fill out the Secret textbox. Use a random string with high entropy (e.g., by taking the output of
ruby -rsecurerandom -e 'puts SecureRandom.hex(20)'at the terminal).
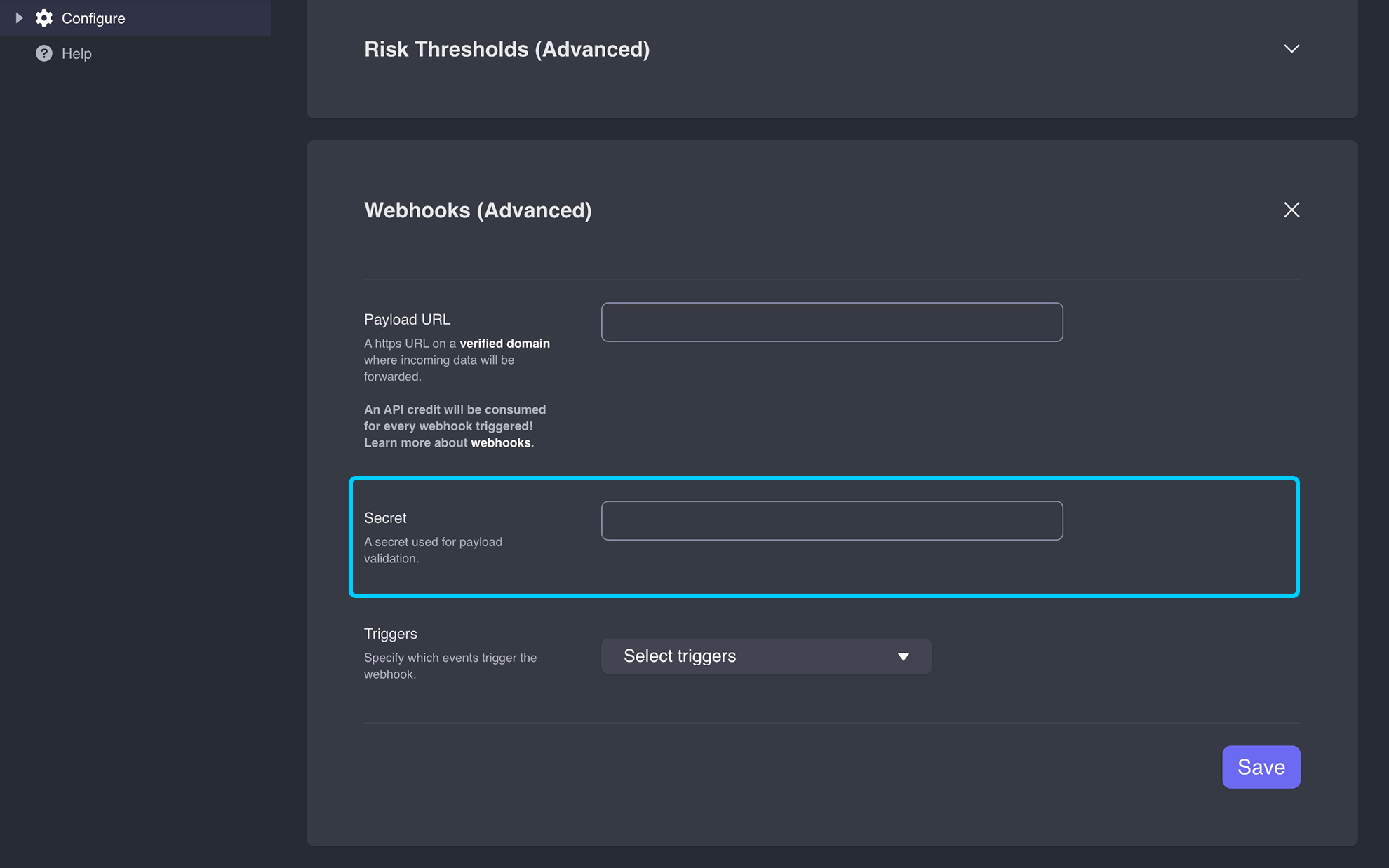
Webhook secret token field - Click Save.
Next, set up an environment variable on your server that stores this token. Typically, this is as simple as running:
$ export SECRET_TOKEN=<em>your_token</em>Never hardcode the token into your app!
#
Validating payloads from Airlock
When your secret token is set, {% data variables.product.product_name %} uses it to create a hash signature with each payload. This hash signature is included with the headers of each request as X-Airlock-Signature.
For example, if you have a basic server that listens for webhooks, it might be configured similar to this:
require 'sinatra'
require 'json'
post '/payload' do
request.body.rewind
push = JSON.parse(request.body.read)
"I got some JSON: #{push.inspect}"
endThe intention is to calculate a hash using your SECRET_TOKEN, and ensure that the result matches the hash from Airlock. Airlock uses an HMAC hex digest to compute the hash, so you could reconfigure your server to look a little like this:
post '/payload' do
request.body.rewind
payload_body = request.body.read
verify_signature(payload_body)
push = JSON.parse(payload_body)
"I got some JSON: #{push.inspect}"
end
def verify_signature(payload_body)
signature = 'sha256=' + OpenSSL::HMAC.hexdigest(OpenSSL::Digest.new('sha256'), ENV['SECRET_TOKEN'], payload_body)
return halt 500, "Signatures didn't match!" unless Rack::Utils.secure_compare(signature, request.env['HTTP_X_AIRLOCK_SIGNATURE'])Note: Webhook payloads can contain unicode characters. If your language and server implementation specifies a character encoding, ensure that you handle the payload as UTF-8.
Your language and server implementations may differ from this example code. However, there are a number of very important things to point out:
No matter which implementation you use, the hash signature starts with
sha256=, using the key of your secret token and your payload body.Using a plain
==operator is not advised. A method likesecure_compareperforms a "constant time" string comparison, which helps mitigate certain timing attacks against regular equality operators.